Lost Crypto Recovery: Can AI Really Crack the Code?
Share IT

Launch Your Dream Website with Us!
Click Here to Get in touch with Us.
Categories
Lost Crypto Recovery
Is AI Able to Break the Code? Deciphering Cryptocurrency Loss Recovery
Numerous individuals view cryptocurrencies as a thrilling, albeit unstable, financial domain. But a large chunk of this digital wealth—which is thought to be worth hundreds of billions of dollars—has vanished from reach. This wealth has been locked away because to lost passwords, hardware malfunctions, or forgotten private keys, posing a significant barrier to both the person and the larger crypto market.
AI and cutting-edge hardware introduce the hopeful heroes.
Lost Crypto Recovery
Thankfully, recent developments in technology are providing hope for those who have misplaced cryptocurrency investments. This revival is principally propelled by the combined strength of:
Table of Contents

AI Models, First:
Lost Crypto Recovery
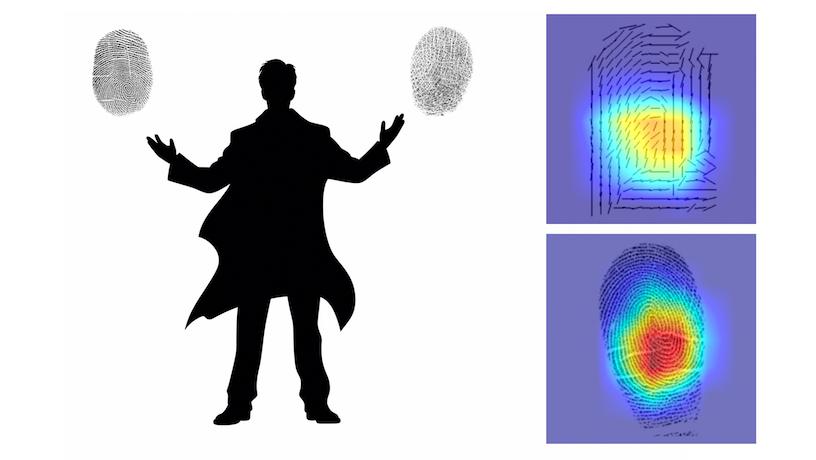
Password and encryption key recovery is being revolutionized by AI models such as PASS-GPT. These models can evaluate patterns and make accurate judgments regarding stolen credentials since they have been trained on large datasets. Artificial intelligence (AI) has the potential to greatly improve recovery rates by recognizing potential vulnerabilities in encryption techniques and by comprehending typical password structures.
- Cutting-Edge Computer Hardware:
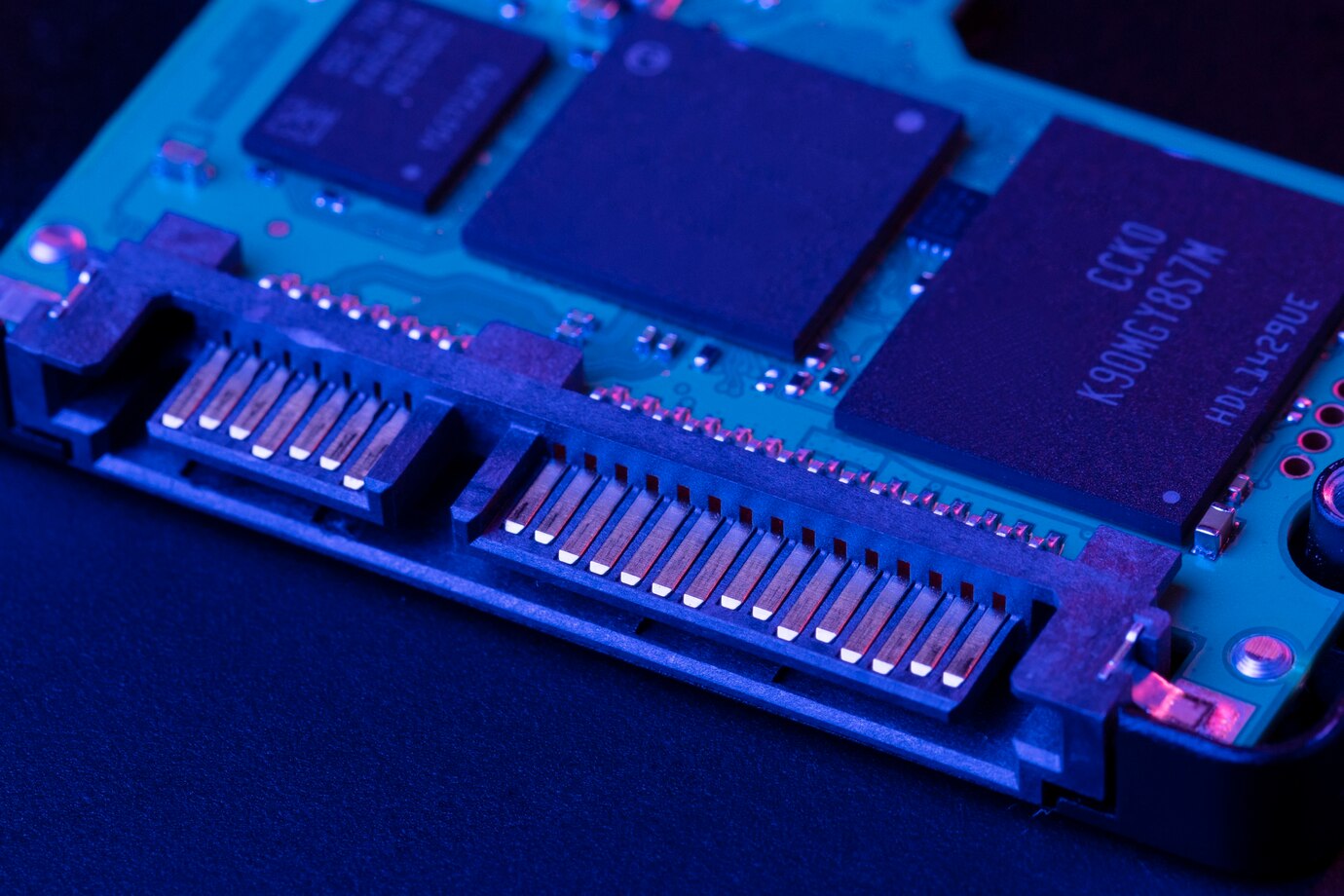
Lost Crypto Recovery: The development of strong CPUs and GPUs (Graphics Processing Units) has made it possible to solve complicated cryptography issues with the processing power they require. These developments in hardware allow algorithms to be executed more quickly and effectively, which cuts down on the amount of time needed for future recovery efforts.
- Cutting Edge Algorithms:
The foundation for protecting digital assets, cryptography, is a field that is always changing. Nevertheless, no system is perfect. Sophisticated algorithms are being developed by researchers expressly to take advantage of weaknesses in the encryption techniques now in use in cryptocurrency wallets. These algorithms provide an extra layer of potential answers, but they are continually changing in tandem with improvements in encryption.
- Attacks using Side Channels:
Side-channel attacks are an unconventional strategy that can be useful for a motivated person. These entail trying to retrieve data while examining minute differences in a device’s behavior, including heat production or power usage. Specialized recovery services may use this technique, however it is generally discouraged and morally dubious. It can also be used in some situations with relevant legal considerations.
- Services for Crypto Recovery:
These specialized services try to recover lost cryptocurrency by utilizing the technology listed above. Usually, their procedure entails examining a number of data points, such as wallet information, previous access attempts, and maybe hardware remains, if they are accessible.
It’s crucial to keep in mind:
- Achievement is not assured: While developments are encouraging, many times successful recovery is questionable due to the complexity of encryption and the possibility of human error when creating passwords.
- Ethics must always come first: Reputable crypto recovery companies ought to follow all legal requirements and conduct themselves morally. Any service should be carefully investigated before sensitive data is entrusted to them.
- Be ready to pay any expenses that may arise: The fees for crypto recovery services are usually high and take the form of a percentage of the money that is recovered. This charge schedule emphasizes how crucial it is to thoroughly consider the possible expenses and success rates before moving forward.
A Hint of Hope but Not a Promise
Lost Crypto Recovery
Unquestionably, the fusion of cutting-edge hardware, AI, and creative algorithms is bringing forth a new era in crypto recovery. But it’s important to approach these developments with a healthy dose of hope. While providing some hope to those who have lost access to their digital assets, it is crucial to give ethical issues top priority, be aware of the limitations of these techniques, and perform extensive due diligence before to working with any service provider.
Lost Crypto Recovery
In the end, keeping regular backups of your private keys and using secure password management are your greatest lines of defense against losing access to your cryptocurrency. You may ensure more control over your significant cryptocurrency holdings and reduce the need for prospective recovery efforts by taking proactive steps to safeguard your digital assets.

Launch Your Dream Website with Us!
Click Here to Get in touch with Us.




















































Recent Comments